From university graduates to seasoned analysts, eSentire’s SOC is building the next generation of cyber talent.
Earlier this summer, I had the opportunity to visit the security operations centre (SOC) of MDR provider eSentire.
The company describes itself as a protector of more than 2,000 organisations in 80 countries, using “advanced technologies, including machine learning and 24/7 threat hunting, to help organisations anticipate, withstand, and recover from cyber-attacks.” Based in the Republic of Ireland, this was not my first SOC visit, but it was my first with some noticeable differences.
Firstly, this is one of a number of global SOCs, offering 24/7 coverage as well as education and mentoring for future analysts.

“It might be one global SOC,” says Ciaran Luttrell, global vice president of SOC Operations at eSentire, “but I feel that we're a very mature operation. The average industry experience here is five years plus, spread across the whole team. Our technical director has been with us for 15 years next month. I've been here ten years, and overall there’s a lot of industry experience, particularly at the management level. So I mentioned 114 analysts, and the rest then will be team leads, managers, directors — that kind of thing.”
He explained that when a new analyst is being hired, they look at the global need and consider where the demand is greatest. For example, if there is a requirement in a certain time zone — between the Irish and Canadian SOCs — they can position the analyst where they are needed.
“We'll interview in tandem in both locations, and we'll pick the best talent. That just makes things better for us, as we get the right people in the door who can work well in this environment.”
Company Feeder
Luttrell also noted that the SOC is very much a feeder to other departments, such as the response units, solutions architecture, and product management.
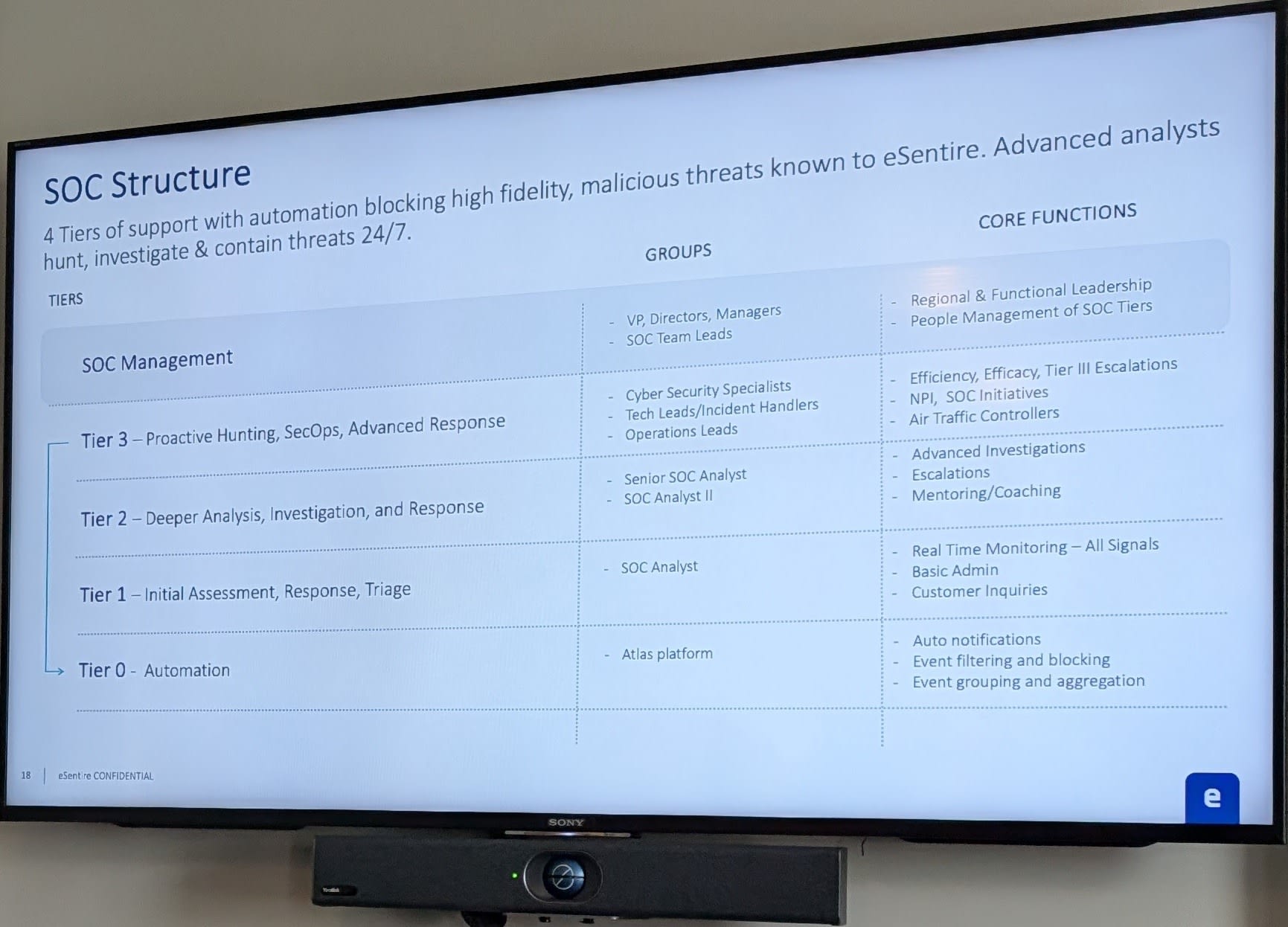
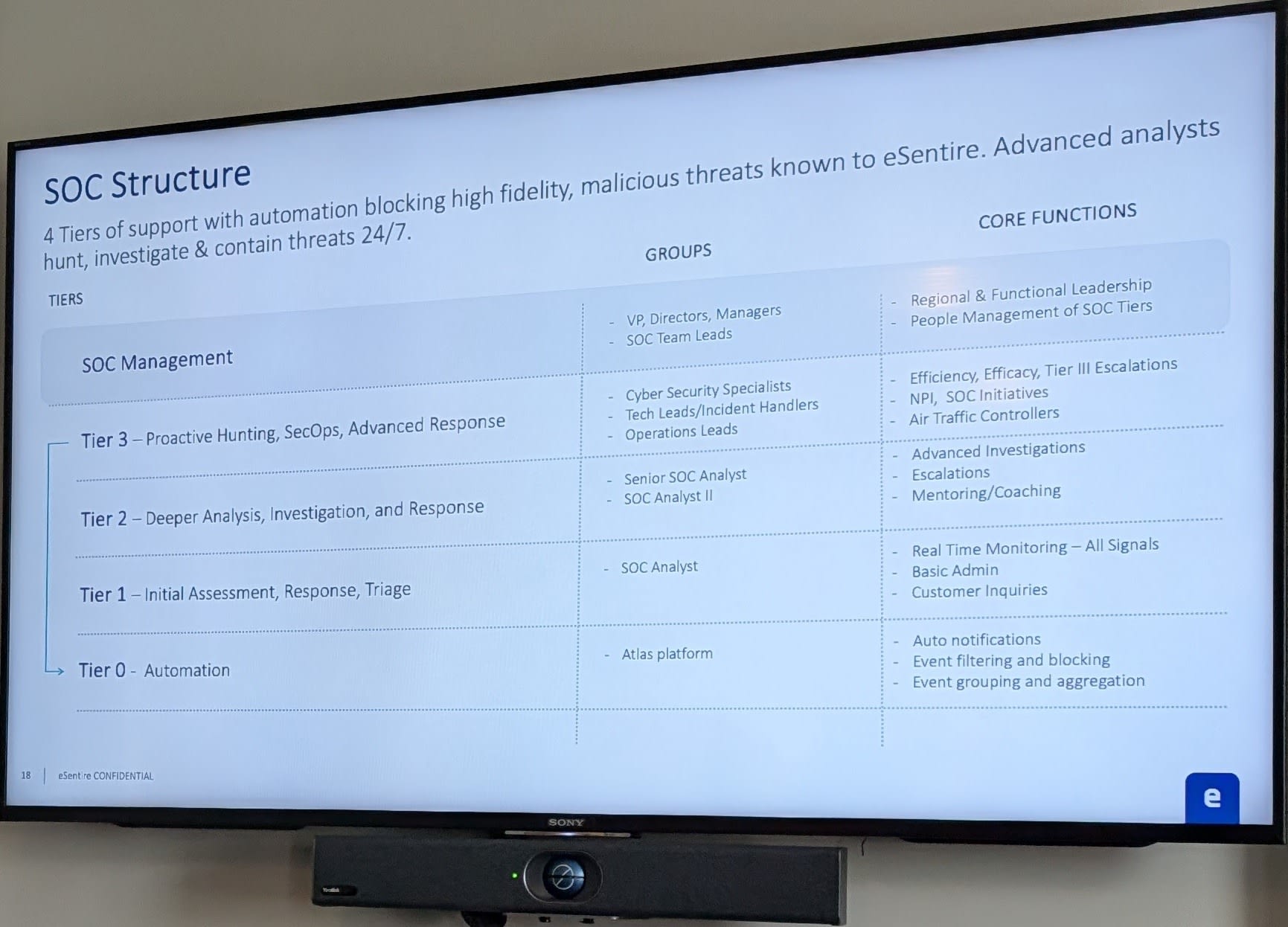
So how does the SOC work within a customer-facing MDR provider? Luttrell said analysts need to be dealing with customers almost from the start, beginning with basic customer inquiries. This involves handling alerts and doing filtering, while much of the more administrative detail has increasingly been handled through automation.
“Of what's involved, probably 80/20 in terms of monitoring versus customer engagement type work — and that changes when you move up the tiers,” he explains. The tiers begin at level one, with opportunities to progress to levels two and three.
Asked if there is training across all tiers, Luttrell described a “soft coaching program” where analysts are taken off daily work for coaching delivered by tier three analysts.
“As a newer analyst, you're going to be requesting enough help and need that kind of assistance to complete end-to-end investigations at this level,” he says. “They might need support, and one of the ways we provide that is through an in-line health function.”
Breeds Talent
Moving on, Luttrell said this SOC is the sort of place that “breeds talent into other parts of the organisation.” He also explained that for each role, relevant external certifications are aligned — from entry-level certifications such as CompTIA and Cyber Essentials, to specialist degrees and senior management-level qualifications.
In terms of hiring, I asked whether they can find enough talent within this part of Ireland — or even Europe — to meet their needs, or whether they must search further afield. Luttrell said that generally, almost all staff are found locally. “We're lucky here in Cork that the universities are good feeders for us, and if not locally, certainly in Ireland. People are willing to relocate for the job they want,” he says.
“People are willing to relocate for the role. We’ve had three or four of those people recently, and in the last six months we've made a big effort around it. We've had people relocate from within Ireland, but generally speaking, the majority are in Cork. We're lucky that Munster Technological University (MTU) has been a big source of talent for us. A lot of people who we would take on as interns end up coming back.”
Asked what qualities stand out in a potential SOC analyst, the team at eSentire cited a genuine passion for learning and a strong interest in investigation.
During my visit, I also met a number of SOC analysts across different tiers — some who had moved from around the world to take up these roles, while others were more local, including graduates from MTU. They spoke of the benefits of exposure to the workplace, gaining hands-on experience, training while working, and investigating live environments.
As I mentioned, this wasn’t the first SOC I’ve visited, but at a time when hiring and finding the right candidates is a challenge across the industry, this felt like a positive example of how to do it right.
Written by
Dan Raywood is a B2B journalist with 25 years of experience, including covering cybersecurity for the past 17 years. He has extensively covered topics from Advanced Persistent Threats and nation-state hackers to major data breaches and regulatory changes.
He has spoken at events including 44CON, Infosecurity Europe, RANT Forum, BSides Scotland, Steelcon and the National Cyber Security Show, and served as editor of SC Media UK, Infosecurity Magazine and IT Security Guru. He was also an analyst with 451 Research and a product marketing lead at Tenable.